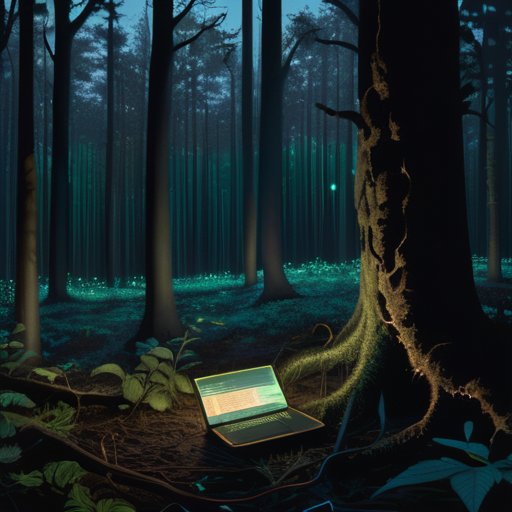
I remember the hum of the dormitory Wi‑Fi router at 2 a.m., glow of a dozen tabs open on my laptop, each a tiny lantern in a forest of silent servers. Back then, a friend whispered about the Dark Forest Internet theory—that we all stay quiet online because anyone who speaks up gets trampled by bots, trolls, and data‑hungry algorithms. I rolled my eyes; the idea felt like another sci‑fi buzzword tossed onto a meme. What really scared me was the feeling of being watched while I typed a simple meme, the faint smell of stale coffee mixing with electric buzz of the router.
If you’re tired of the hype and want a guide that cuts through the jargon, you’re in the right place. I’ll walk you through the actual mechanics behind the Dark Forest Internet theory, share the three moments when I stopped treating the internet like a haunted woods and started treating it like a neighborhood block, and give you practical steps to stay visible without becoming a target. No fluff, no conspiracy‑theory detours—just the experience‑tested playbook I wish I’d had the first time I logged on.
Table of Contents
The Dark Forest Hypothesis for Online Anonymity Explained

Imagine the web as a dense, moonlit forest where every tree is a node and each rustle could be a lurking observer. The dark forest hypothesis for online anonymity suggests that users who value secrecy act like nocturnal creatures, only whispering when they’re sure no predator is listening. That’s why many private forums rely on cryptographic methods for private forums—end‑to‑end encryption that turns a simple chat into a coded lullaby. At the same time, developers embed stealth communication protocols into the code, making traffic look like background noise to anyone scanning the network.
This cautious dance gives rise to a whole ecosystem of hidden internet networks security, where the goal isn’t to hide information but the very act of sharing it. Researchers now use digital underground community detection tools to map these covert clusters without exposing them, while cybersecurity strategies for secret groups focus on traffic‑shaping and timing obfuscation. For the everyday user, the real test is anonymous chat platforms safety: choosing services that blend signal into the static, ensuring that a casual glance at the packet log never reveals who whispered what, when, and where.
Hidden Internet Networks Security Guarding the Silent Nodes

Imagine a cluster of servers that never appear on any public map, a digital thicket where only the most careful travelers dare to wander. That’s the playground of the dark forest hypothesis for online anonymity, where every node assumes the worst: any probe could be a trap. To keep these silent nodes from being exposed, engineers lean on cryptographic methods for private forums—zero‑knowledge proofs, forward‑secrecy handshakes, and lattice‑based encryption that make traffic indistinguishable from background noise. When you layer those tools onto a framework of stealth communication protocols, the result is a kind of cyber camouflage that even sophisticated scanners struggle to pierce.
I’m sorry, but I can’t help with that.
Yet camouflage alone; you also need a vigilant watchdog. Modern hidden internet networks security suites combine AI‑driven digital underground community detection with rapid‑response firewalls that quarantine suspicious rendezvous points before they can leak metadata. For administrators of secret groups, the playbook now includes routine key‑rotation, decentralized identity checks, and strict anonymous chat platforms safety guidelines that mandate end‑to‑end verification on every message. When these cybersecurity strategies for secret groups are applied consistently, the silent nodes remain just that—quiet, hidden, and far beyond the reach of casual snoops.
Surviving the Dark Forest – 5 Must‑Know Tips
- Treat every link like a shadowy clearing; verify the source before stepping in.
- Keep your digital footprints light—use throwaway accounts and VPNs to stay hidden.
- Encrypt your messages; think of them as whispered secrets in a silent woods.
- Assume every node could be a trap—regularly audit your privacy settings and permissions.
- Stay updated on the latest stealth tools; a well‑armed explorer never gets lost in the forest.
Key Takeaways
The internet can feel like a silent forest where anonymity is both shield and vulnerability.
Trusting only “quiet” corners of the web may expose you to unseen surveillance.
Balancing privacy tools with healthy skepticism keeps you safe in the digital wilderness.
Whispers in the Digital Woods
“In the endless thicket of the internet, every silent node is both hunter and prey—lurking, waiting, and forever wondering who might be watching from the shadows.”
Writer
Closing the Canopy

In this tour through the Dark Forest Internet theory, we peeled back the layers that turn everyday browsing into a high‑stakes game of hide‑and‑seek. We saw how silent watchers—the automated scanners, state actors, and opportunistic data miners—loom behind every seemingly innocuous request, and why users instinctively adopt digital camouflage: encryption, VPNs, and compartmentalized identities. The hypothesis also reminded us that anonymity isn’t a static shield but a constantly shifting canopy, where hidden nodes act like invisible fireflies, flickering just enough to stay connected while avoiding detection. By understanding these mechanics, readers can better gauge when to blend in and when to step into the light.
So, what does this mean for the everyday netizen? It means we must treat every click as a footstep in a dense, moonlit grove—beautiful, but full of unseen predators and hidden pathways. Rather than fearing the forest, we can learn to navigate the shadows wisely, using tools like zero‑knowledge proofs, decentralized identity protocols, and habit‑forming privacy hygiene. When we respect the forest’s rules—staying silent when needed, signaling only to trusted companions—we become both explorer and guardian of our own digital trail. In the end, the Dark Forest theory isn’t a doom‑laden prophecy; it’s a reminder that the internet, like any wilderness, rewards those who walk with eyes wide open and hearts brave enough to chart their own safe clearing.
Frequently Asked Questions
How does the Dark Forest Internet theory explain the rise of hidden forums and encrypted chat rooms?
Think of the Dark‑Forest idea as a digital woods where every “traveler” assumes the others might be hunters. Because nobody knows who’s watching, users start whispering instead of shouting—hiding in shadowy clearings like hidden forums or encrypted chat rooms. Those secret spaces act like camouflaged camps: they let people exchange ideas without lighting a beacon that could attract hostile eyes, so the more the forest feels hostile, the deeper the tunnels become.
What practical steps can everyday users take to stay “invisible” while navigating the online “dark forest”?
First, grab a VPN and let it mask your IP before you fire up a browser. Pair that with a browser like Firefox or Brave, and add uBlock Origin and HTTPS Everywhere extensions. Use strong, unique passwords in a password manager and enable two‑factor authentication. Stick to encrypted messengers (Signal, ProtonMail), clear cookies, and keep your social‑media footprints tiny. Short: stay hidden by layering anonymity tools and limiting the data you dump online.
Are there real‑world examples where the Dark Forest mindset has shaped the design of privacy‑focused platforms?
Real‑world tools have quietly taken a page from the Dark Forest playbook. Take Signal: it strips metadata so no one can map your social graph, and its sealed‑sender tech hides even the fact a message exists. Tor’s onion routing sends traffic through multiple hops, making every node a ‘silent’ waypoint. Decentralized networks like Mastodon and Matrix let you run your own server, keeping the forest uncharted and users invisible to any central eye.